What is Intruder?
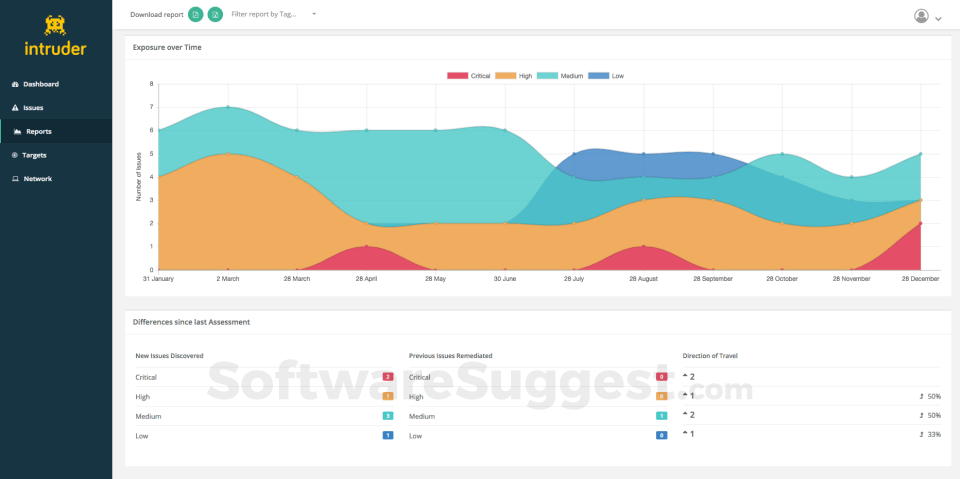
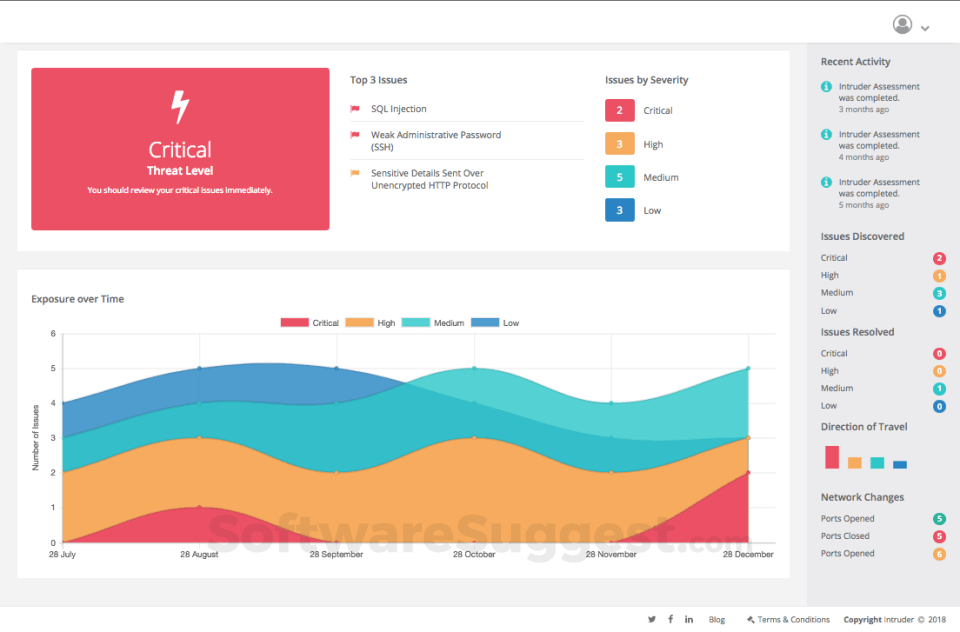
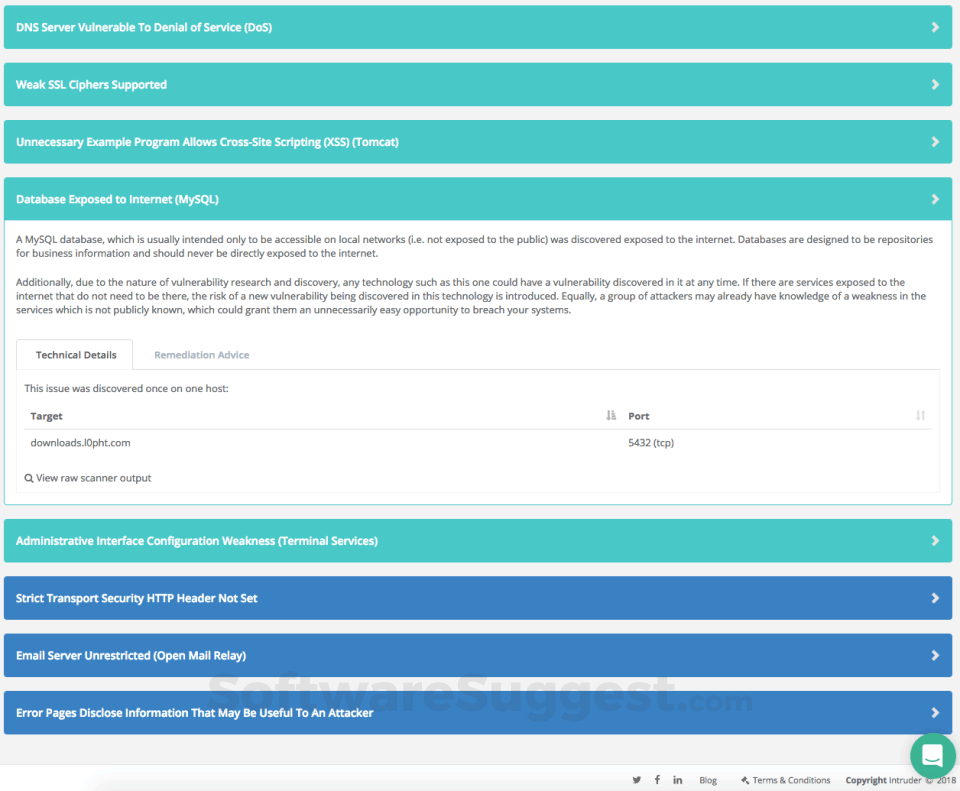
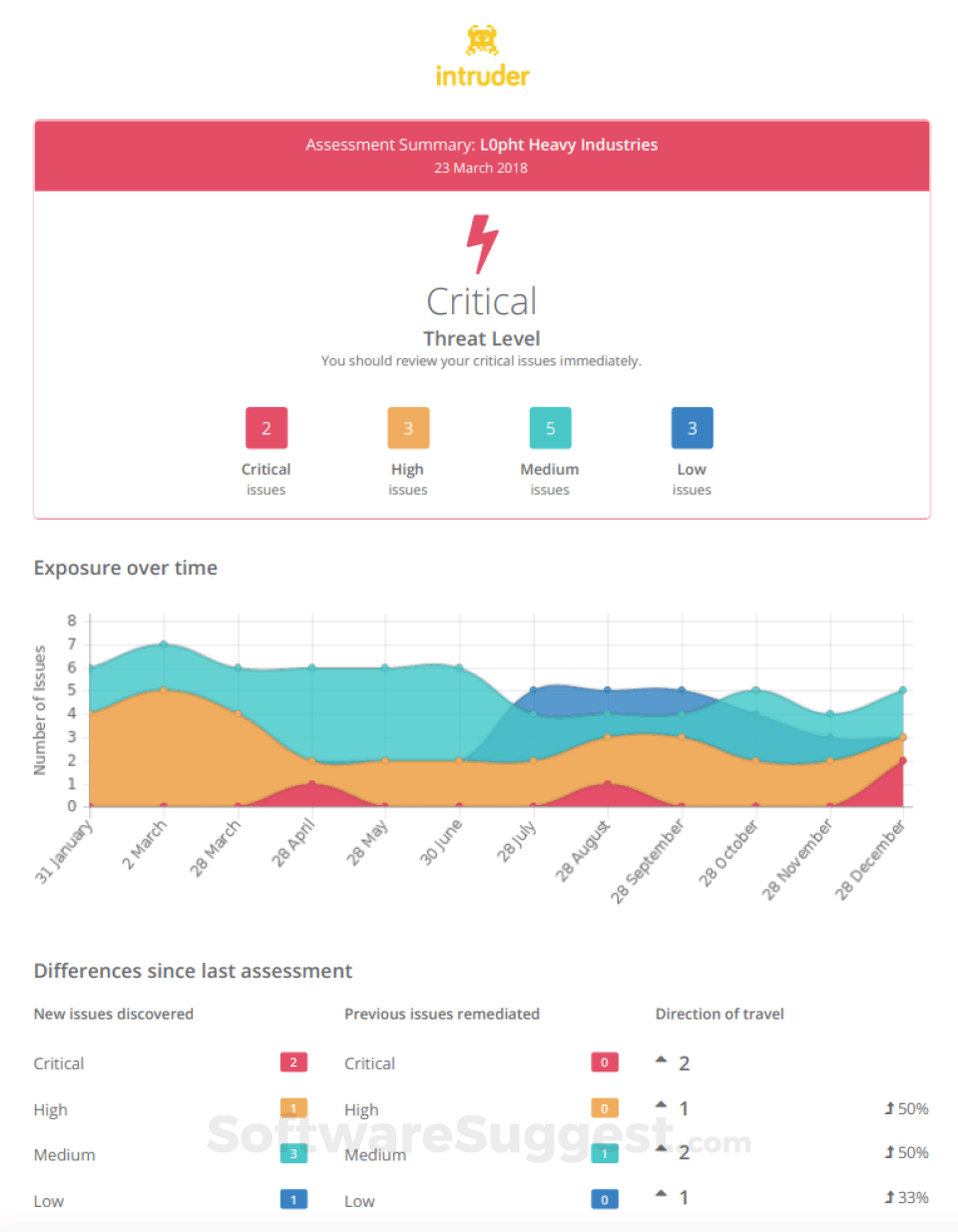
Intruder is a fully featured Security Management Software designed to serve Agencies, Enterprises. Intruder provides end-to-end solutions designed for Web App. This online Security Management system offers Two-Factor Authentication, Vulnerability Scanning, Risk Management, Prioritization, Web Scanning at one place.
Intruder Starting Price
$ 38/Per Month

Our Awards and Recognition
Talk with a software expert for free. Get a list of software that's great for you in less than 10 minutes.
Key Features of Intruder
Here are the powerful features that make Intruder stand out from the competition. Packed with innovative tools and advanced functionalities, this software offers a range of benefits.
- Access control
- Activity Log
- Activity Monitoring
- Advanced Firewall
- AI / Machine Learning
- Anonymous Browsing
- Anti Spam
- Anti Virus
- Application Access Control
- Application Security
- Archiving
- Asset Discovery
- Asset Tagging
- Audit Trail
- Audit Trails
- Availability Testing
- Activity Log
- AI / Machine Learning
- AI Security
- Anti Virus
- Anti-Spyware
- Antivirus
- Application Security
- Asset Discovery
- Asset Tagging
- Audit Trail
- Behavioral Analytics
- Biometric
- Blue Team Tools
- Compliance Management
- Compliance Reporting
- Content Caching
- Asset Discovery
- Asset Tagging
- Asset Discovery
- Asset Tagging
- Compliance Reporting
- Compression
- Continuous Backup
- Database Security Audit
- Diagnostic Tools
- IOC Verification
- Local Server Options
- Maintenance Scheduling
- Multiple System Support
- Network Scanning
- Patch Management
- PCI Assessment
- Access control and user authentication
- Anti-spam protection
- Blacklist monitoring and removal
- Bot detection and mitigation
- Compliance with industry security standards
- Content security policy enforcement
- Cross-site scripting (XSS) protection
- Data encryption in transit and at rest
- DDoS protection
- File Integrity Monitoring
- IP blocking and whitelisting
- Login protection and brute-force attack prevention
- Malware scanning
- Real-time threat detection
- Reputation monitoring
- Secure API integration
- Brute-Force Attack Simulation
- Command Execution Testing
- Compliance Testing
- Continuous Monitoring and Testing
- Cross-Site Scripting (XSS) Testing
- Denial of Service (DoS) Testing
- Directory Traversal Testing
- DNS Spoofing
- Exploit Generation
- File Inclusion Testing
- Firewall and Intrusion Detection System (IDS) Testing
- Malware Analysis
- Man-in-the-Middle (MitM) Attacks
- Multi-Platform Support
- Network Mapping
- Password Cracking
Intruder Pricing
Here are the pricing plans for Intruder. Choose the plan that best fits your requirements and budget. Get Detailed Intruder pricing as per your requirements.
- Scheduled monthly assessments
- Checks for over 10,000 security vulnerabilities including WannaCry and Heartbleed
- Up to 2 user accounts
- All features in Essential
- Run additional scans on demand
- Emerging threat notifications
- Checks for Web Application flaws such as SQL Injection and Cross-Site Scripting
- Network view
- AWS, Google Cloud, Azure Cloud Connectors
- Slack and Jira integration
- Unlimited user accounts
- All features in Pro
- Hybrid penetration testing helps identify issues beyond the capabilities of automated scans
- Access to technical advice from our expert penetration testers
- Free Cyber Essentials certification
- PCI ASV scans available
- Bug Bounty validation
Intruder Specifications
Get a closer look at the technical specifications and system requirements for Intruder. Find out if it's compatible with your operating system and other software.
Intruder Comparisons
Compare Intruder with other similar options available in Security Management Software. Explore the key differences to see why it's the top choice for businesses and individuals.

Intruder Reviews (0)
No reviews yet. Rate this app or be the first to review.
Write a ReviewAlternatives of Intruder
Explore alternative software options that can fulfill similar requirements as Intruder. Evaluate their features, pricing, and user feedback to find the perfect fit for your needs.
Intruder FAQs
How much does Intruder cost?
The starting price of Intruder is ₹ 2736/Per Month. It has different pricing plans:
- Essential : ₹ 2736/Per Month
- Pro : ₹ 12960/Per Month
- Verified : ₹ 32400/Per Month
The details of Intruder’s free trial have not been shared by the vendor.
What are the top 5 features for Intruder?
The top 5 features for Intruder are:
- Risk Management
- Two-Factor Authentication
- Vulnerability Scanning
- Prioritization
- Patch Management
What type of customer support is available from Intruder?
The available support which Intruder provides is: